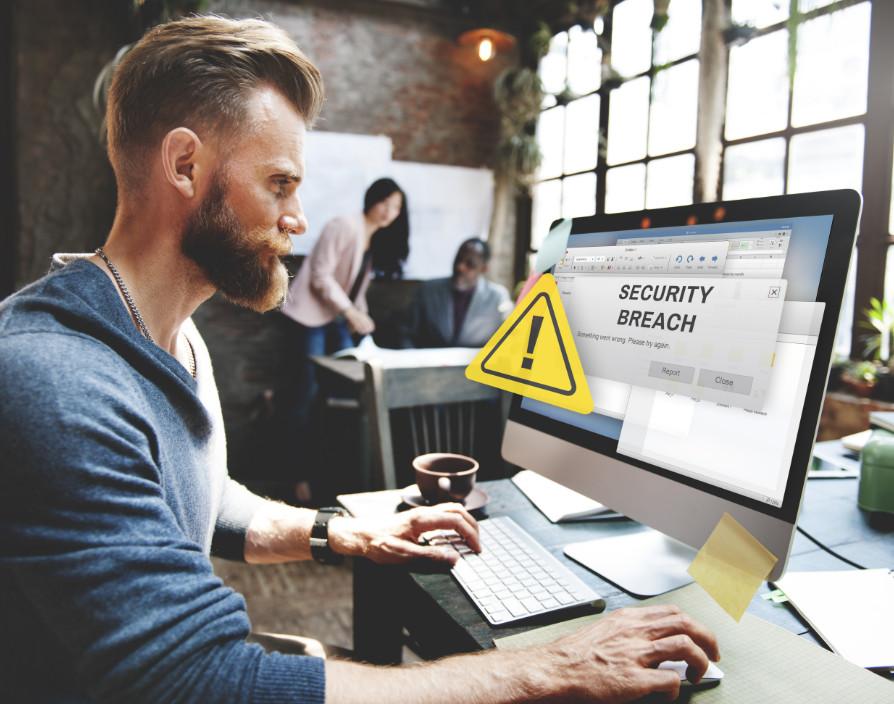
Data privacy and protection laws require businesses to store and handle data of employees, customers and account holders safely. As technology advances, cybercrime has increased circumventing traditional safeguards commonly through malware, phishing and man-in-the-middle attacks. Cybercriminals often seek ransom payments from businesses. These data breaches can evoke regulatory sanctions such as financial penalties and reputational damage to the business.
How to plan for ransom requests
Ransom requests are alarming and intimidating and there is no conclusive procedure to follow. Firstly, regulators do not recommend that the company pay these requests; often it incentivizes attackers to target your business again, and does not guarantee the return of the stolen data. There is a myriad of options the company can undertake following a ransom request, the most effective solution is prepared for this situation – businesses should prepare an effective data breach and notification policy and cyber security incident response plan allowing for swift and decisive actions to be taken to minimise the breach.
Businesses should keep in mind that sensitive data is subjected to more onerous legal protections due to its vulnerable nature, and must be processed with higher security measures to prevent the identification of data subjects. If this data is acquired in a cyberattack, the repercussions would be more significant – to the business and to the data subjects.
The most practical preventative measure would be regularly maintaining security systems through internal and planned testing to reveal vulnerabilities in security and company response plans. Businesses should consult their supply chains to ensure third parties and contractors maintain equivalent diligent security standards. Regular engagement and training should be undertaken to ensure those in the business navigate the infrastructure correctly to comply with systems securely. Especially where sensitive data is concerned, stringent control and access management procedures should be implemented to afford a higher level of security.
Once a real attack has occurred, forensic investigators could be engaged in seeking to trace the perpetrators, though; in practice, this is extremely difficult given the anonymity and decentralized nature of cyber adversary organisations and global networks. An appointed media handler could be utilised to navigate the fallout following a breach and minimise the disruption to the business’s reputation. These communications also require notification to individuals whose data has been compromised where the risk to them is high. Further reporting under the General Data Protection Regulation requires reports of breaches to the Information Commissioner’s Office, which is detrimental to the rights of individuals, generally 72 hours after the business is aware of the breach.
The value of injunctions
Some businesses may be wary of seeking an injunction as it admits to the public that a breach has occurred drawing a degree of negative publicity, however, injections can be significantly valuable in preventing the distribution of unlawful destruction, loss, alteration, unauthorised disclosure of, or access to, data. Seeking the powers of the court at an adolescent stage can be invaluable in mitigating the impact of the breach, default judgements and final injunctions have been granted even without a hearing. Illustrating the court’s willingness to aid victims of cyber-attacks through expedient relief, businesses are encouraged to act quickly as it is possible for an injunction to be granted the same day of the request.
The courts have deployed these powers to extend outside of the jurisdiction, by granting global freezing orders against persons unknown. Furthermore, in the case of PML v Persons Unknown [2018] EWHC 838 (QB), where a firm obtained an interim non-disclosure order on behalf of a UK company, under the protection of anonymity, after it sustained a major cyber-attack. Here the court went further by piercing the cloak of anonymity that cybercriminals operate behind by requiring delivery up and the destructing of the stolen data, thus requiring identification of the perpetrator.
Claimants have been able to preserve their anonymity in proceedings where they have been awarded a permanent injunction in a summary judgement. Derogation from traditional open justice highlights to victims that the option of injunctions should be seriously considered, even when reputational damage is a concern and the perpetrator is absent from the litigation proceedings.
The proliferation of cybercrime is expected to increase as technology continues to integrate as a fundamental aspect of everyday life and the pinnacle of most businesses. Victims of cybercrime and bodies seeking to prevent attackers, readily welcome the significance of new case law and increasing jurispendence in the cybercrime sphere.
It cannot be stressed enough that the most effective solution in preparation for cyberattacks is for businesses to have an effective data breach and notification policy and cyber security incident response plan. Legal experts who specialise in data protection and cybersecurity in an employment context are not only best suited but are also well-positioned in preparing effective policies and procedures that help businesses navigate cybersecurity and handle cyberattacks in a swift and decisive manner.
Share via: